Drift’s Contagion Loop: From Operational Breach to Market Drain
A breach in control infrastructure, layered dependencies, and capital routing frameworks turned a single exploit into a network event.
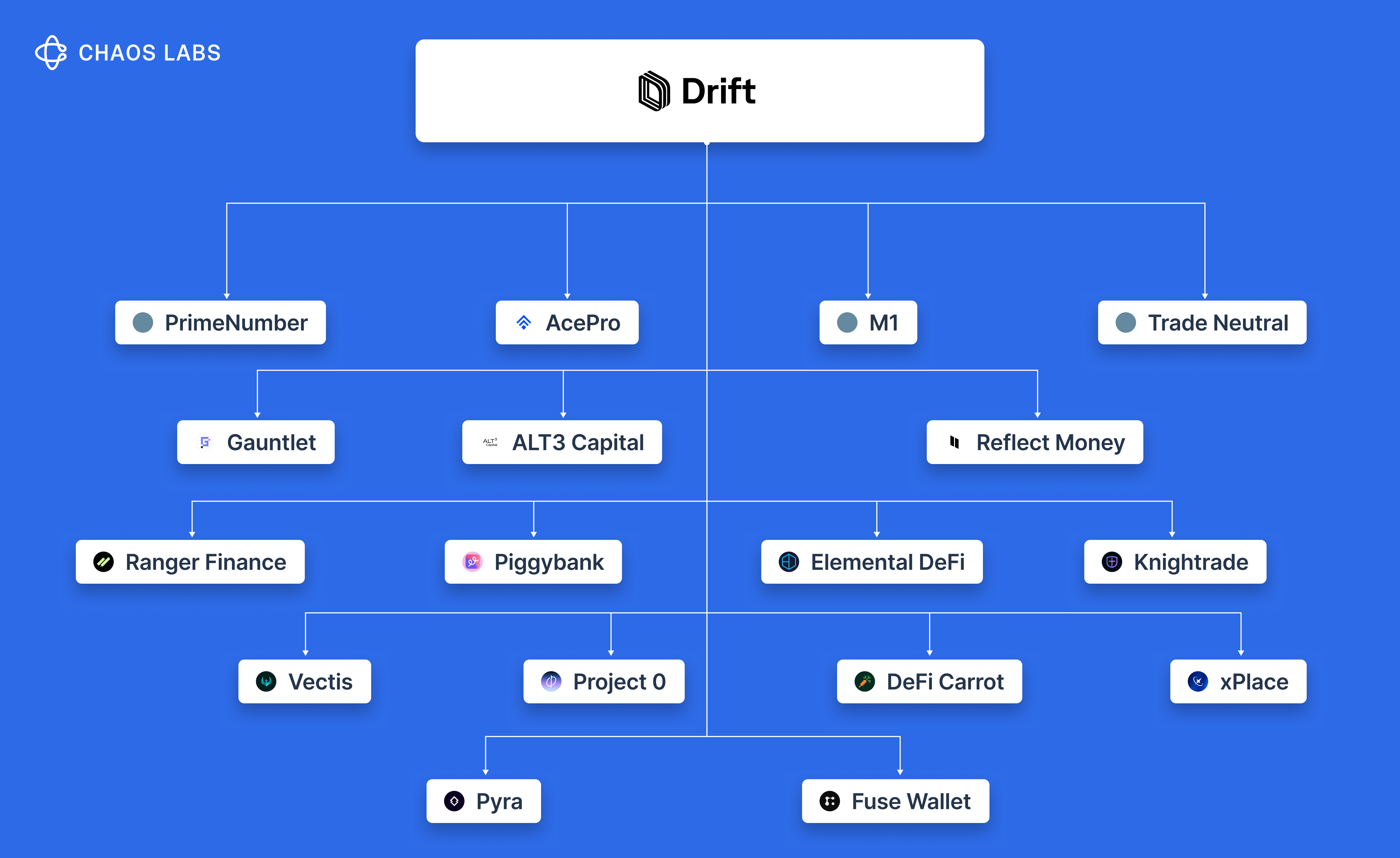
Drift’s exploit has quickly evolved into a broader contagion event, forcing protocols, vaults, and users across Solana DeFi to reassess their exposure under time pressure and with incomplete information.
- Prime Number held over $10M through Drift vault strategies.
- Gauntlet retained ~$6.4M in residual allocations on deprecated vaults.
- Reflect Money froze redemptions on USDC+ and USDT+, with at least $1.95M exposed.
- TradeNeutral reported ~$3.67M affected across select strategies.
- Elemental DeFi saw ~$2.9M in combined exposure across lending and fixed deposits.
Additional protocols, vaults, and aggregators confirmed exposure, but there is still no final tally, as dependencies embedded within yield products and allocation strategies are surfacing in real time.
How did we get here?
DeFi continues to frame risk primarily through the lens of smart contract security; however, a quick check of the Rekt leaderboard shows otherwise.
A meaningful share of losses has originated from the control layer around protocols, including multisigs, custody systems, admin permissions, and signing infrastructure, as well as economic vectors such as oracle manipulation and governance capture. Smart contracts define one boundary of failure, while the effective attack surface extends across every mechanism that governs how state changes propagate.
Drift’s exploit sat within this broader surface.
Where are the risks?
A review of the current top 20 exploits provides a clear distribution.
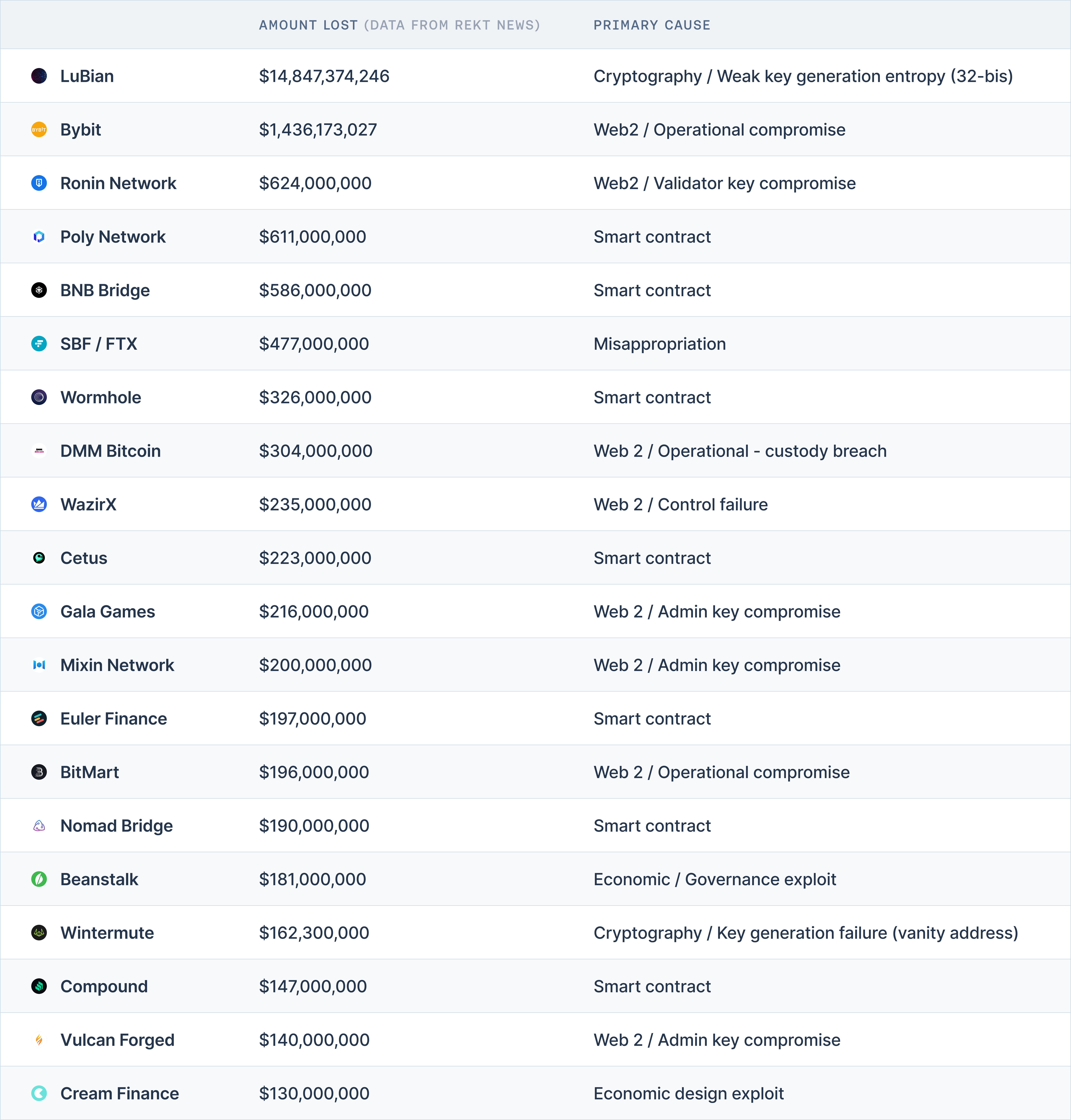
A few points to note: LuBian was linked to a broken cryptography theft, and FTX was outright misappropriation and fraud. Excluding these, the remaining 18 incidents provide a more accurate view of how losses are distributed.
- Approx 55% are operational or security-linked exploits, including admin key compromises and control breaches
- Approx 37% are smart contract exploits
- Note: this gap widens when measured by capital lost, with operational failures totaling ~$3.35B, nearly 50% higher than the ~$2B lost through smart contract exploits
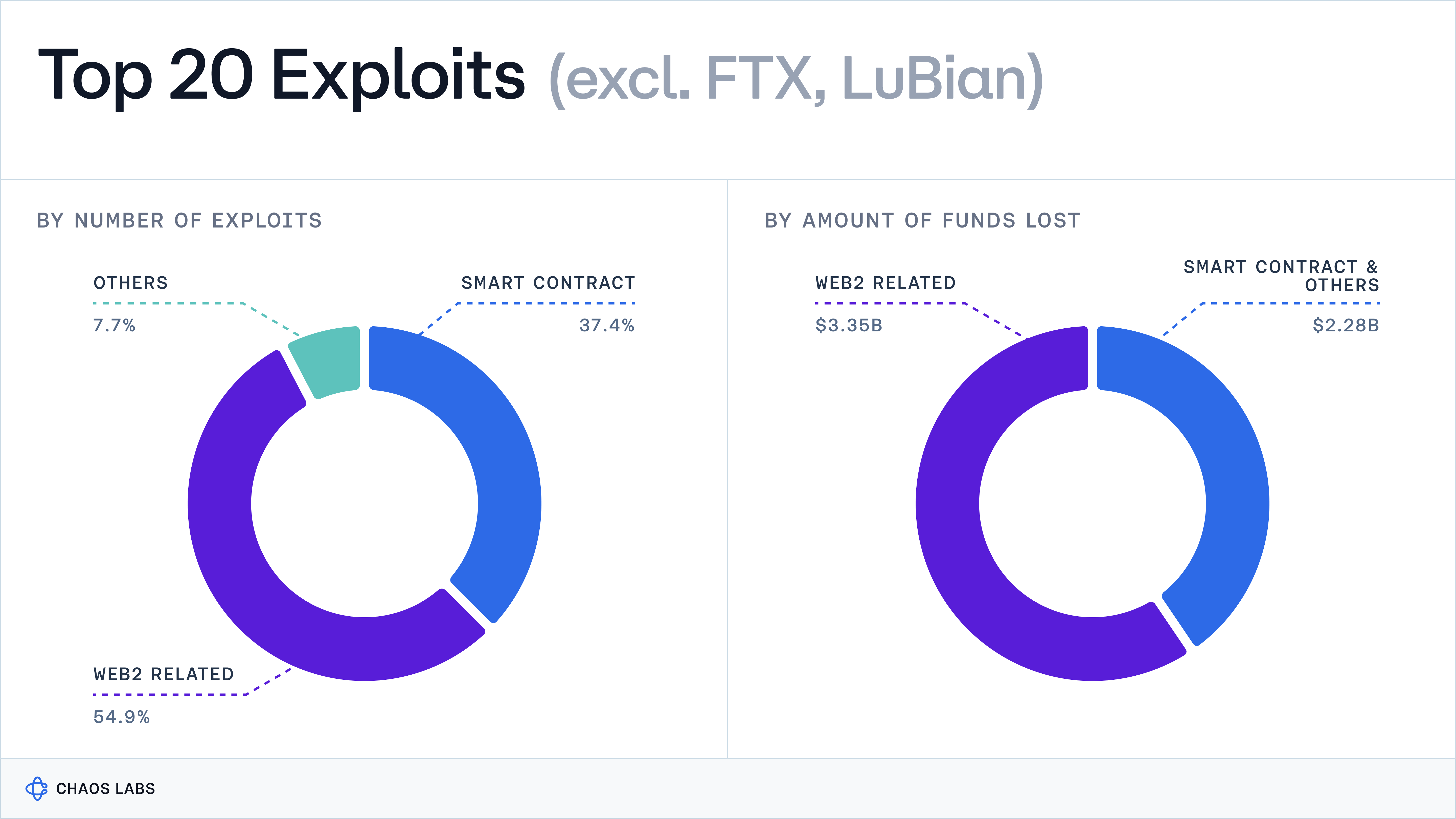
Extending this analysis further down the Rekt leaderboard would likely widen this gap, given that operational controls and security processes tend to weaken in early-stage DeFi protocols and exchanges. A key point is that DeFi’s composability expands the attack surface through integrations, as external dependencies introduce additional entry points for risk.
Drift’s Contagion Loop
The contagion loop: localized issues become system-wide risk through the structure of the system itself.
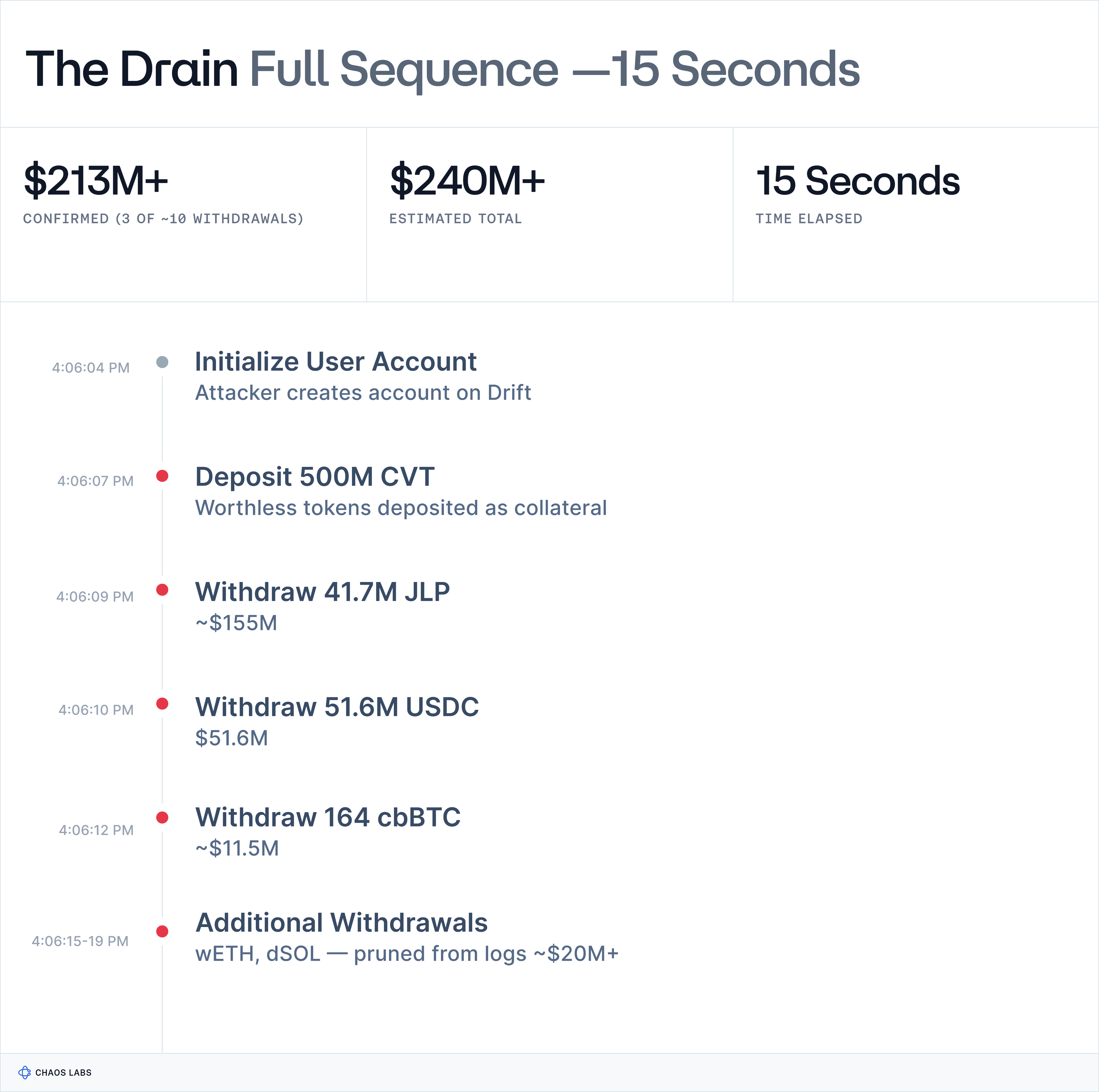
In the case of Drift, the attacker exploited a multisig transition (to a new setup with a 2-of-5 threshold and no timelock) to gain admin access to the protocol, either through compromised private keys or social engineering. This granted full control over market creation, oracle assignment, and withdrawal parameters, allowing the attacker to introduce a malicious asset, manipulate pricing, and drain funds within seconds.
The attack was planned for multiple weeks, as the token used in the exploit was created 20 days ago.
This contagion spread across Solana DeFi through direct vault deployments, collateral exposure, borrow-lend integrations, and products that relied on Drift as an underlying yield engine.
A few protocols have already communicated and quantified their exposure, while a few other protocols have only confirmed that they are affected, without disclosing the size or structure of that dependency. The situation remains fluid, and both exposure estimates and loss figures are likely to evolve as positions are unwound and dependencies are mapped more precisely.
Here’s a tally as of April 2nd, 10 AM EST:
- Drift: All funds deposited across borrow/lend, earn, vaults, and trading represent the primary exposure. This is the origin point of the event, with many downstream protocols, OCCAs, and risk curators allocating into Drift’s vault and earn strategies.
- PrimeNumber: Exposure via Drift vaults, primarily JLP Hedge Vault and Bit Wealth, $10m+
- Gauntlet: Exposure via Drift vaults, including hJLP, hJLP 2x, and dSOL Plus. The related strategies were deprecated in February 2026, though not all users withdrew already their deposits, $6.4m
- AcePro: Exposure via Drift vaults, mainly Ace Pro Steady D05, $1.05m
- ALT3 Capital: Exposure via Drift vaults, primarily ETH Gain and USDC Yield, $1.1m
- M1: Exposure across two Drift vaults, approximately $520k
- Reflect Money: USDC+ and USDT+ affected, with mint and redemption frozen. At least $1.95m in USDC+ appears exposed, though actual exposure may be lower given multi-venue allocation. Exponent Finance Reflect markets also affected, around $525k
- Trade Neutral: Select vaults and strategies affected, while NT Vaults remain unaffected per protocol communications. Estimated exposure of $3.67m, with Perena indirectly impacted
- Ranger Finance: rUSD exposed to Drift, representing approximately 6% of TVL, or $919k
- Piggybank: Approximately 2.6% of funds deployed to Drift, around $106.4k
- Elemental DeFi: Drift used within USDC vaults, with approximately $224k in USDC lend and $2.7m in SOL fixed deposits affected
- Knightrade: JLP delta-neutral strategies affected, with withdrawals frozen. Exposure up to $3.05m
- Vectis: UltraX and DriftPack vaults report exposure of 25% ($822.5k) and 48% ($866k) respectively
- Project 0: Protocol fully paused after accepting borrows against Drift-linked collateral. Loss socialization under consideration. Total exposure undisclosed. TVL approximately $104.6m, though majority is not Drift-related
- DeFi Carrot: Boost and Turbo products unaffected. Remaining protocol exposed via Earn and CRT strategies. Disclosed exposure of $16.8m, though direct Drift dependency remains unclear
- xPlace: Savings product relied on Drift for yield. Protocol frozen. Exposure not disclosed
- Pyra: Drift used across its entire borrow/lend stack. All funds in that segment affected. Exposure not disclosed
- Fuse Wallet: Earn functionality affected. Exposure not disclosed
DeFi Dev Corp’s (DFDV) Solana DAT was initially thought to be affected following last year’s announced integration with Drift. The company later clarified that it was not impacted by the exploit.
Even excluding that exposure, currently available figures suggest the impact on Solana DeFi could approach 5.5% of total TVL, or more than $300 million when including Drift’s direct losses.
Conclusion
Drift’s exploit reinforces that risk in DeFi does not stop at smart contracts.
The largest exploits in crypto have consistently originated from the layers around the smart contracts, i.e., signer setups, admin controls, operational processes, custody systems, and economic design.
This event is also a stark reminder of the double edge of composability. While it improves capital efficiency and expands product design choices in stable conditions, it could also convert into a transmission channel, carrying risk across protocols faster than it can be assessed. Understanding where funds are deployed, which dependencies sit underneath, and how those dependencies behave when they fail is no longer optional; visibility at the moment of disruption determines the ability to respond.
This is why dependency mapping sits at the core of how we are building Chaos AI. Our core objective is always to surface hidden exposures and trace propagation paths in real time, before losses cascade.
The Market Crypto Never Built
Crypto never built the infrastructure layer that makes financial systems safe enough to deserve the trust people place in them. Without a forcing function, the industry spends on protection as if it's optional while losing billions to exploits it could have prevented.
Five Levels of Agentic Finance
Finance has more data than it can process. This piece breaks down the five levels of agentic finance, from static data access to fully autonomous operation, and where most AI products actually sit today.
Risk Less.
Know More.
Get priority access to the most powerful financial intelligence tool on the market.